Emerging Vehicle Technologies And The Future Of Security Compliance
Meiran Galis is the CEO & cofounder of Scytale. He is an expert in security compliance and passionate about helping SaaS companies grow.
getty
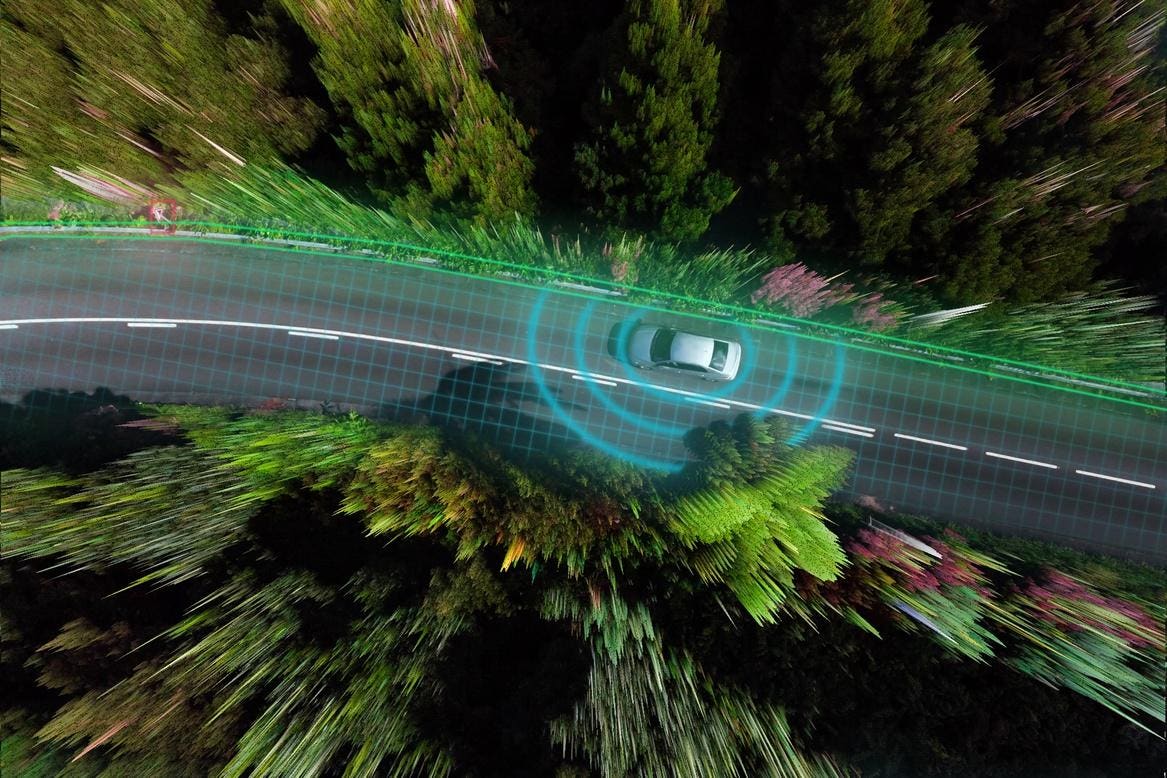
Do you think Henry Ford could ever have imagined the comfort and simplicity drivers today can enjoy? Probably not. The idea of self-driven cars would have sounded like an H.G. Wells fantasy.
Yet here we are—on the brink of that fantasy.
And even though the delayed arrival of autonomous vehicles on the consumer market is still something of a sore point, it may be a good thing when you consider the security risks that still need to be addressed in their deployment.
The Connected Drive: A Double-Edged Sword
Modern vehicles serve as interconnected data hubs thanks to technologies like cellular, Bluetooth and Wi-Fi. These features provide convenience, enabling real-time navigation, hands-free calling and mobile hotspots for passengers.
However, this connectivity introduces vulnerabilities, inviting cyber threats and privacy breaches. Hackers can exploit weaknesses to access vehicle systems, posing safety risks.
With features like personal profiles, vehicle control, life risk and location tracking in the fray, the implementation of security control by the design of features such as access control, encryption and intrusion detection systems is now a regular part of the automotive industry.
But up to now, these risk precautions have been to protect the privacy of drivers and passengers for the most part. Yet what happens when the risk extends to the very infrastructures that surround road safety and the automotive industry?
The Security Risks That Await The Automated Vehicle Industry
The automated vehicle industry is poised for transformation, promising seamless integration with digital ecosystems and enhanced mobility. But the transition brings with it cyber threats that could lead to very real harm. Just imagine having your vehicle “hijacked” and crashed from a remote location. It’s not a future you’d be too eager to get to.
The Threat Within
As vehicles become more reliant on digital infrastructure, the risk of insider threats and data breaches is always present. The departure of key personnel with critical access or knowledge could result in the leakage or stealing of sensitive information or the exploitation of backdoors, potentially compromising the security of millions of people driving smart vehicles.
Feeding Off Data Vulnerability
Connected vehicles serve as data hubs, collecting vast amounts of information about their users’ behaviors and preferences. This is the very data that’s eagerly sought by cybercriminals and presents opportunities for exploitation. From data scraping in junkyards to unauthorized access by hackers, the potential for misuse is significant, posing privacy and security concerns for vehicle owners, all the way to death.
Exploiting The Gaps In Software Updates
The implementation of over-the-air software updates through cloud infrastructure opens up new avenues for cyberattacks. Hackers could exploit compromised receiving devices to install malicious updates, leading to widespread malware attacks that can compromise the vehicle’s autonomy and introduce unauthorized control of vehicles. Without robust security measures, vehicles and passengers could be made vulnerable to manipulations.
Extending The Risk To The Greater Network
Seamless connectivity between vehicles and smart devices offers convenience but also introduces increased security gaps. The threats and security gaps on a smart device can lead to malicious access into vehicle networks, compromising user data and potentially affecting vehicle operations. The intersection of critical and non-critical vehicle systems creates vulnerabilities that could be exploited to manipulate vehicle behavior or disrupt operations.
How can this be stopped?
The Road Ahead: Safeguarding Automated Vehicles From Cybersecurity Threats
In the pursuit of seamless integration between smart devices and automated vehicles, the industry faces a critical challenge: cybersecurity. Tesla already offers services that allow users to effortlessly order, unlock and direct a communal autonomous vehicle from their smartphones. It’s the peak of automotive convenience.
But that convenience also opens the door to malicious attacks.
In a sophisticated cyberattack scenario, an attacker deceives an individual into installing a surveillance application on their smartphone, which then harvests personal and vehicle-related data. Leveraging this information, the attacker gains unauthorized access to the autonomous vehicle’s network through vulnerabilities in its telematics control unit.
Once inside, they deploy malicious code capable of two alarming actions: silently broadcasting sensitive information such as real-time location and passenger identities back to the attacker, and injecting false sensor data into the vehicle’s system.
This manipulation of sensor inputs, crucial for the vehicle’s decision-making, could lead to disaster, including causing the vehicle to misinterpret its surroundings and potentially lead to a crash.
Before autonomous vehicles become a commercial commodity, a proactive plan needs to be in place to keep drivers and passengers’ privacy and lives safe.
Creating An Industry-Wide Security Standard
First, implementing data security standards like those used in payment processing can safeguard vehicle electronics and data storage. Additionally, forming diverse industry consortia, similar to the Automotive Information Sharing and Analysis Center, fosters collaboration and information sharing across sectors.
Centralizing Oversight And Governance
Drawing inspiration from successful industry models like the Bluetooth Special Interest Group, the automotive industry could establish an oversight entity to govern connected and autonomous vehicle technologies. This entity would certify products for compliance and enforce standards through rigorous monitoring.
Introducing Baseline Safety Feature Protocols
While creating such a framework demands collaboration among developers, it promises significant benefits. By agreeing on baseline features and ensuring a robust safety process, the industry can ensure the safety and integrity of autonomous vehicles in our increasingly digital world.
As autonomous vehicles become more common on public roads, the goal must be to create a harmonized framework that ensures the safe, secure and ethical deployment of AVs worldwide, balancing innovation with public safety and privacy concerns.
The crucial next step has to be the establishment of comprehensive and effective autonomous vehicle standards with the collaboration of industry stakeholders, regulatory bodies and international organizations.
H.G. Wells’s future of flying cars is close at hand. Are we ready for it? Not by a long shot. But with the safety of the public at stake, this is one time when regulations really can’t afford to lag behind the introduction of new tech any longer.
Forbes Technology Council is an invitation-only community for world-class CIOs, CTOs and technology executives. Do I qualify?


